Welcome back to the Ethical Reckoner. In this Weekly Reckoning, we cover a grave injustice that (for once) wasn’t perpetrated by AI. But don’t worry, we’ll also talk about AI in the context of this big election year, and then dive into some of the invisible infrastructure that makes the Internet possible.
This edition of the WR is brought to you by: the Australian Open’s extremely advanced water removal technology.
The Reckonnaisance
Hundreds of British postal workers prosecuted due to faulty IT system seeing justice thanks to a TV show
Nutshell: Over 16 years, 700 British Post Office workers were convicted of financial crimes because their accounting system reported false shortfalls. A TV show is prompting action to exonerate them.
More: Although concerns were raised for years about the system, which lunched in 1999, the Post Office refused to acknowledge that the system was defective (it apparently didn’t record money from lottery sales or cash machine transactions) and instead forced postal workers to make up the shortfalls themselves, often prosecuting them as well. People were imprisoned, went bankrupt, and even committed suicide. There was court case after court case, eventually resulting in an official inquiry and compensation program, but only 93 convictions had been overturned. A TV show about it, “Mr. Bates vs. the Post Office,” began airing earlier this month and created such an outcry that UK PM Rishi Sunak promised a law to exonerate and compensate all victims. Adding this one to my watch list.
Why you should care: It’s great that they’re being compensated, but this is too little, too late for many of the victims. Justice shouldn’t take a viral TV show to achieve. But also, this shows that it’s not just advanced AI systems that we need to worry about. Even “dumb” software can cause real harm if it’s created dumbly and implemented in a dumb, rigid system. As a software engineer, I certainly coded my fair share of bugs, but there are procedures (like automated testing) that can help—and I would argue are the moral responsibility of programmers and software companies to use.
OpenAI says no to election disinformation, yes to the Pentagon
Nutshell: OpenAI made two announcements: one, they’re implementing measures to counter election disinformation; and two, they’re removing “military and warfare” from their list of prohibited applications and contracting with the Pentagon.
More: On the elections side, OpenAI is (finally) going to implement provenance credentials for DALL-E so we’ll theoretically be able to tell when an image has been generated, even if it’s been modified. They’re also going to integrate with more real-time news reporting and, in the US, CanIVote.org to provide authoritative information about news and election procedures.
At the same time, the company quietly dropped its blanket ban on working with the military, although it still says that its systems shouldn’t be used to “harm yourself or others,” such as by developing or using weapons. This change seemed to be prompted by news that they’re working with the US military on “national security use cases that align with our mission,” including on cybersecurity tools.
Why you should care: As we face down the biggest global election year in history with deepfakes of politicians already spreading, ChatGPT could become the most authoritative source of election information online—certainly more so than social media, and potentially more than even Google if it gets clogged with other AI-generated crap (already happening on e-commerce sites)—which could create a bitterly ironic situation where generative AI has set itself up as both the problem and the solution. At the same time, OpenAI could be getting itself into a sticky situation; there’s a long history of tech workers protesting when their companies start working with militaries, including Google’s Pentagon AI contract, Microsoft’s Army HoloLens contract, and Google and Amazon’s joint cloud contract with the Israeli military.
US and China hold back-channel talks on AI
Nutshell: Last year, representatives from OpenAI, Anthropic, and Canadian AI company Cohere secretly met with Chinese AI experts to discuss AI risk and AI safety investments.
More: The talks, organized by a “private mediation organization,” took place in Geneva with the knowledge of the US and Chinese governments. They were apparently successful, with plans for future meetings.
Why you should care: The US and China are… not happy with each other right now, which makes cooperation on AI difficult. It’s good that some sort of communication is happening. That being said, the fact that North American representatives seemed to be entirely industry actors is concerning, as is the fact that the talks were mostly about AI safety (which should not be our primary focus) and creating an international regulatory body (which should not be our only hope).
Chad’s Internet service almost entirely taken out by hackers
Nutshell: The hacking group Anonymous Sudan claimed credit for the attack, which caused Internet traffic to collapse for periods over two days.
More: Anonymous claimed the attack was protesting the government’s support of the Sudanese RSF paramilitary group (currently involved in a civil war in Sudan). The attack highlights the fragility of Chad’s Internet infrastructure; they have poor transit provider and ISP diversity, meaning that people—if they’re connected at all—are highly vulnerable to outages.
Why you should care: While it’s notable that Anonymous has the power to degrade an entire country’s Internet access, to me, one of the striking parts of this story was that only 18% of Chad’s population actively uses the Internet, which is below average for the region—but the average in Africa is 39%, and other countries’ Internet resilience isn’t much better than Chad’s. As much as we like to complain in the US about how terrible our ISPs are, at least we have them. It’s a reminder that the tech-imbued world that we take for granted is not universal, and a reminder to me to keep my research in perspective.
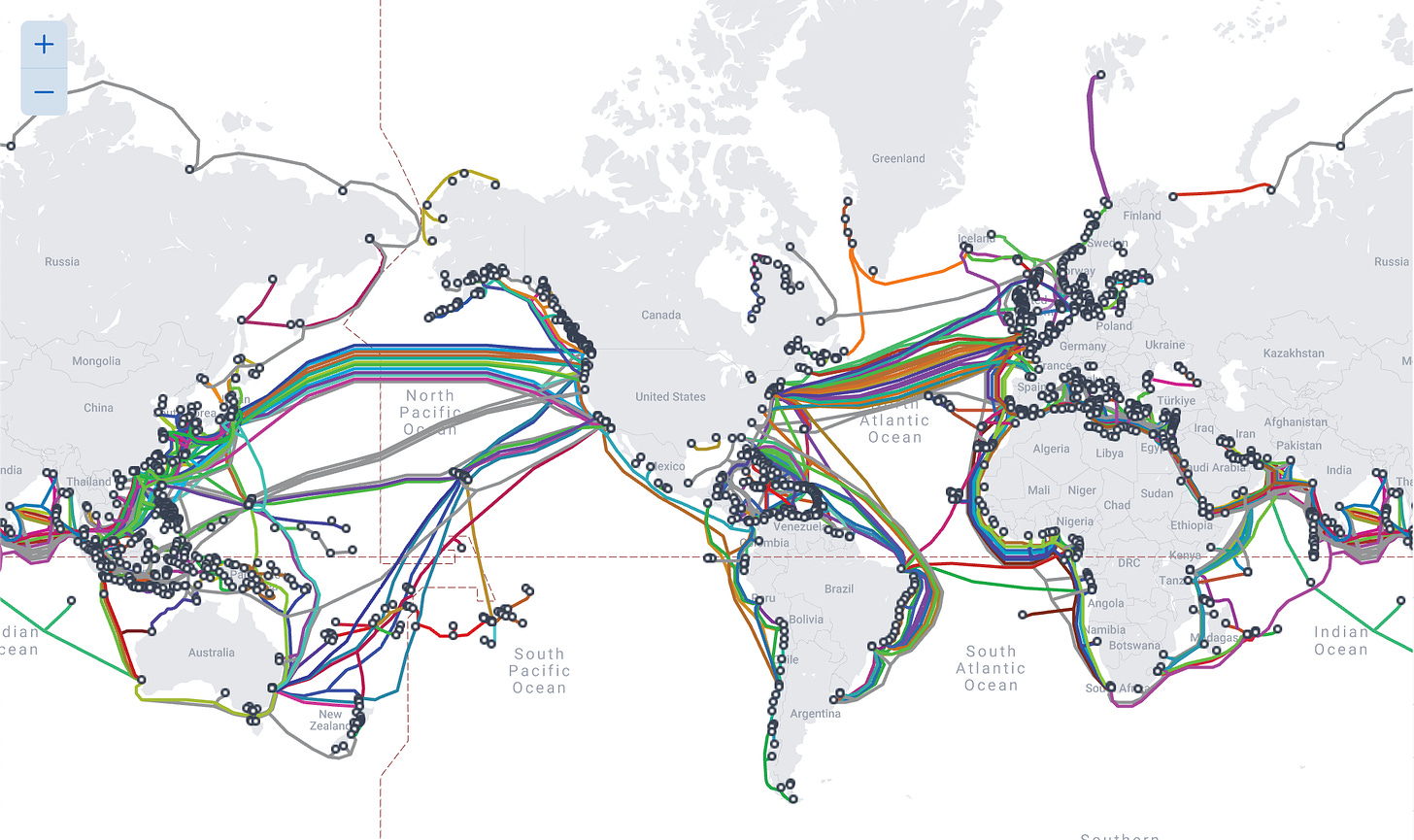
Extra Reckoning
Did you know that 99% of Internet traffic is carried through cables under the sea? Even “wireless” services like 4G rely on submarine cables to integrate with the global Internet infrastructure. Some colleagues from the Yale Digital Ethics Center and I have a pre-print out about submarine cables and digital sovereignty (available here) and it’s gotten me thinking about the invisible infrastructure that supports our lives—which is one of the reasons why I found the Chad Internet attack so interesting. These cables are so important, but most people think about them not at all, and the international regulatory regime seems to think about it just as little.
Not every country has equal access to the global Internet infrastructure. Coastal countries control the cable landing points and the first few miles of the cables themselves, which they don’t actually have any legal obligation to maintain. Though it’s generally in their strategic interest to keep them safe, it can sometimes be in the strategic interest to cut them—as China was accused of doing to the only two cables connecting a Taiwanese island to the Internet, highlighting the importance of cable redundancy. They also sometimes have a strategic interest in tapping them for espionage, which is shockingly easy because the cables are basically undefended, especially in international waters.. Because of this, cables are also often accidentally damaged, but only Australia and New Zealand seem to be doing a good job of actively preventing fishing boats and trawlers from chopping cables.
Companies are the other big players; 59% of cables are owned by the private sector, and companies like Google use the possibility of cable investment to gain lobbying power in countries like Nigeria. This also gives them the ability to favor their own traffic, potentially violating net neutrality with few consequences because of the transnational dynamics. The influence does go both ways, though—countries can influence their flagship companies through regulation, tax breaks, etc., and use them to influence other countries. But, since the countries that have the power (and companies with the power) to lay these cables are generally wealthier nations, there are data colonialism aspects at play as well—developing, landlocked countries basically have no choice but to play ball.
This all has implications for digital sovereignty, which sounds wonky but is basically how countries exert control over the digital: data/software/hardware/infrastructure/etc. Just like countries that control oil/gas pipelines have leverage over other countries, countries that control submarine cable infrastructure also do. However, since submarine cables cross the ocean, other countries can access them in international waters. Fun fact: it’s assumed that many countries are tapping cables and gathering encrypted data in the hopes that quantum decryption techniques will allow them to eventually read it!
You may not care about the political science dynamics of this all, and that’s fine (if you do, read the full paper). Chances are, you live in a country with lots of cable connectivity and redundancy, so your Internet connection may never be impacted by cable issues. But, if you’re interested in global geopolitics, you should know that your country might be using control over these cables to flex their power. There’s a lot of invisible technological infrastructure that impacts our lives, and it’s better to be aware of it to be informed digital citizens and avoid being caught by surprise.
I Reckon…
that Taylor Swift might be the savior of my thesis.
Thumbnail image generated by DALL-E 3 via ChatGPT with the prompt “please make an abstract painting of a map of submarine internet cables”.